mirror of
https://codeberg.org/forgejo/forgejo.git
synced 2025-06-01 20:32:11 +00:00
Add user webhooks (#21563)
Currently we can add webhooks for organizations but not for users. This PR adds the latter. You can access it from the current users settings. 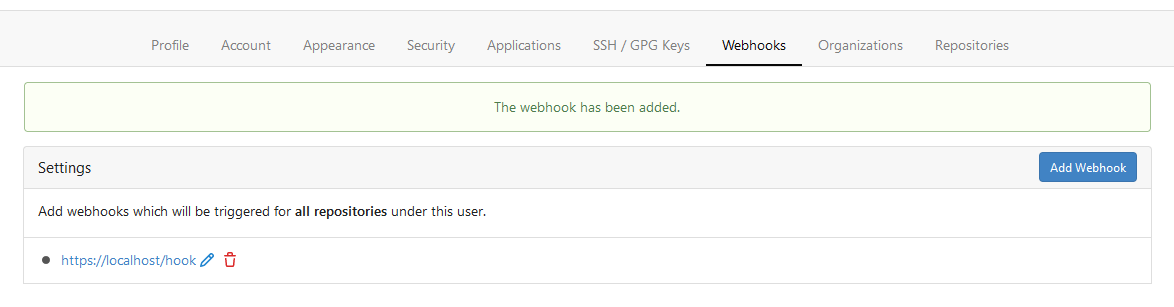
This commit is contained in:
parent
dad057b639
commit
2173f14708
28 changed files with 737 additions and 234 deletions
|
|
@ -32,6 +32,8 @@ const (
|
|||
|
||||
AccessTokenScopeAdminOrgHook AccessTokenScope = "admin:org_hook"
|
||||
|
||||
AccessTokenScopeAdminUserHook AccessTokenScope = "admin:user_hook"
|
||||
|
||||
AccessTokenScopeNotification AccessTokenScope = "notification"
|
||||
|
||||
AccessTokenScopeUser AccessTokenScope = "user"
|
||||
|
|
@ -64,7 +66,7 @@ type AccessTokenScopeBitmap uint64
|
|||
const (
|
||||
// AccessTokenScopeAllBits is the bitmap of all access token scopes, except `sudo`.
|
||||
AccessTokenScopeAllBits AccessTokenScopeBitmap = AccessTokenScopeRepoBits |
|
||||
AccessTokenScopeAdminOrgBits | AccessTokenScopeAdminPublicKeyBits | AccessTokenScopeAdminOrgHookBits |
|
||||
AccessTokenScopeAdminOrgBits | AccessTokenScopeAdminPublicKeyBits | AccessTokenScopeAdminOrgHookBits | AccessTokenScopeAdminUserHookBits |
|
||||
AccessTokenScopeNotificationBits | AccessTokenScopeUserBits | AccessTokenScopeDeleteRepoBits |
|
||||
AccessTokenScopePackageBits | AccessTokenScopeAdminGPGKeyBits | AccessTokenScopeAdminApplicationBits
|
||||
|
||||
|
|
@ -86,6 +88,8 @@ const (
|
|||
|
||||
AccessTokenScopeAdminOrgHookBits AccessTokenScopeBitmap = 1 << iota
|
||||
|
||||
AccessTokenScopeAdminUserHookBits AccessTokenScopeBitmap = 1 << iota
|
||||
|
||||
AccessTokenScopeNotificationBits AccessTokenScopeBitmap = 1 << iota
|
||||
|
||||
AccessTokenScopeUserBits AccessTokenScopeBitmap = 1<<iota | AccessTokenScopeReadUserBits | AccessTokenScopeUserEmailBits | AccessTokenScopeUserFollowBits
|
||||
|
|
@ -123,6 +127,7 @@ var allAccessTokenScopes = []AccessTokenScope{
|
|||
AccessTokenScopeAdminPublicKey, AccessTokenScopeWritePublicKey, AccessTokenScopeReadPublicKey,
|
||||
AccessTokenScopeAdminRepoHook, AccessTokenScopeWriteRepoHook, AccessTokenScopeReadRepoHook,
|
||||
AccessTokenScopeAdminOrgHook,
|
||||
AccessTokenScopeAdminUserHook,
|
||||
AccessTokenScopeNotification,
|
||||
AccessTokenScopeUser, AccessTokenScopeReadUser, AccessTokenScopeUserEmail, AccessTokenScopeUserFollow,
|
||||
AccessTokenScopeDeleteRepo,
|
||||
|
|
@ -147,6 +152,7 @@ var allAccessTokenScopeBits = map[AccessTokenScope]AccessTokenScopeBitmap{
|
|||
AccessTokenScopeWriteRepoHook: AccessTokenScopeWriteRepoHookBits,
|
||||
AccessTokenScopeReadRepoHook: AccessTokenScopeReadRepoHookBits,
|
||||
AccessTokenScopeAdminOrgHook: AccessTokenScopeAdminOrgHookBits,
|
||||
AccessTokenScopeAdminUserHook: AccessTokenScopeAdminUserHookBits,
|
||||
AccessTokenScopeNotification: AccessTokenScopeNotificationBits,
|
||||
AccessTokenScopeUser: AccessTokenScopeUserBits,
|
||||
AccessTokenScopeReadUser: AccessTokenScopeReadUserBits,
|
||||
|
|
@ -263,7 +269,7 @@ func (bitmap AccessTokenScopeBitmap) ToScope() AccessTokenScope {
|
|||
scope := AccessTokenScope(strings.Join(scopes, ","))
|
||||
scope = AccessTokenScope(strings.ReplaceAll(
|
||||
string(scope),
|
||||
"repo,admin:org,admin:public_key,admin:org_hook,notification,user,delete_repo,package,admin:gpg_key,admin:application",
|
||||
"repo,admin:org,admin:public_key,admin:org_hook,admin:user_hook,notification,user,delete_repo,package,admin:gpg_key,admin:application",
|
||||
"all",
|
||||
))
|
||||
return scope
|
||||
|
|
|
|||
|
|
@ -40,8 +40,8 @@ func TestAccessTokenScope_Normalize(t *testing.T) {
|
|||
{"admin:gpg_key,write:gpg_key,user", "user,admin:gpg_key", nil},
|
||||
{"admin:application,write:application,user", "user,admin:application", nil},
|
||||
{"all", "all", nil},
|
||||
{"repo,admin:org,admin:public_key,admin:repo_hook,admin:org_hook,notification,user,delete_repo,package,admin:gpg_key,admin:application", "all", nil},
|
||||
{"repo,admin:org,admin:public_key,admin:repo_hook,admin:org_hook,notification,user,delete_repo,package,admin:gpg_key,admin:application,sudo", "all,sudo", nil},
|
||||
{"repo,admin:org,admin:public_key,admin:repo_hook,admin:org_hook,admin:user_hook,notification,user,delete_repo,package,admin:gpg_key,admin:application", "all", nil},
|
||||
{"repo,admin:org,admin:public_key,admin:repo_hook,admin:org_hook,admin:user_hook,notification,user,delete_repo,package,admin:gpg_key,admin:application,sudo", "all,sudo", nil},
|
||||
}
|
||||
|
||||
for _, test := range tests {
|
||||
|
|
|
|||
Loading…
Add table
Add a link
Reference in a new issue